Wipe An Android Device Remotely?
SIM stands for Subscriber Identity Module, and it’s a removable card inside your cell phone that stores data unique to its user.
SIM is an abbreviation for Subscriber Identity Module, and it is a removable card inside your cell phone that stores data specific to its owner. It basically tells your wireless provider who you are and allows you to connect to their network. You can’t access your data or make phone calls without it, so you’re stuck with WiFi.
A SIM card is an integrated circuit intended to securely store the international mobile subscriber identity number and its related key, which are used to identify and authenticate subscribers on mobile telephony devices.
Because the SIM card contains your identifying information, you can easily transfer it from phone to phone to access the same network and phone number. SIM cards contain data that allows mobile service providers to link physical mobile devices to individual customer accounts. The cards look like credit cards and hotel key cards, but they have integrated circuits printed on them. SIM cards enable phones to send and receive calls and messages, as well as assist service providers in accurately tracking billing for their customers.
a SIM (Subscriber Identity Module) card is a tiny, portable memory chip that stores information about you as a cell phone user. On it, there’s a seventeen-digit code that designates its country code of origin, the system carrier (such as AT&T or Verizon), and a unique user ID.
You may wonder, “Who cares about this code?” A valid question and guess what: phone carriers do. It’s how they attribute cell phone bills and charge us.
Above all else, SIM cards are super handy because they can be easily transferred from one device to another. Just like in my opening story, all that you’d need to do is take it out of one phone and slip it into the new one. By making the switch, most (if not all) of your contacts and personal settings will transfer with it, making life all the easier.
SIM cards were introduced all the way back in 1991. The first SIM card was about the size of a credit card. Since then, there have been several updates and iterations, making them smaller and smaller.
This evolution closely aligns with the history of the GSM (Global System of Mobile Communications) mobile network. Developed to describe protocols for second generation (2G) (3G) (4G) AND (5G) cellular networks, the GSM today stands as the default global standard for mobile communications.
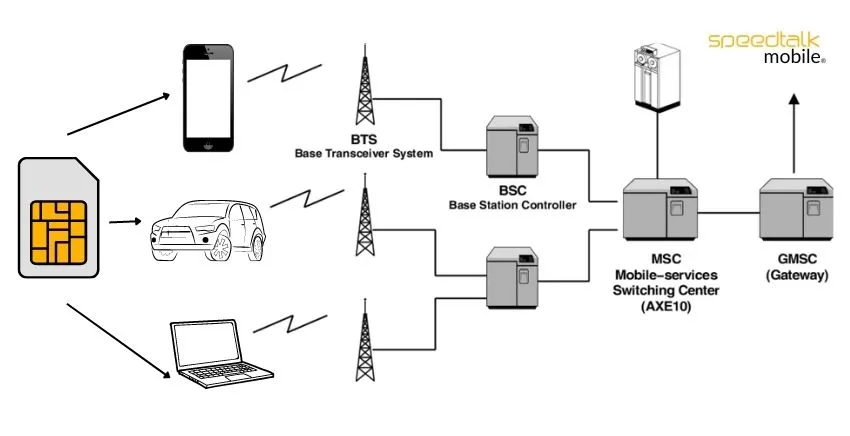
SIM cards are a crucial part of GSM networks, storing user information required for authentication. Ultimately, this allows both your phone to connect with a GSM network and GSM networks to track your phone usage (specifically, your minutes, texts, data usage, etc), giving carriers the information to send you an accurate phone bill.
GSM is the standard network in America, Europe, Asia, Africa, and most other places. Interestingly, besides GSM, the United States has an additional network called CDMA (Code Division Multiple Access) that is used by carriers such as Verizon and Sprint. Phones on the GSM or CDMA network can use any carrier’s network, lowering the costs for the carriers and its users.
When it comes to your phone’s connection with either network, SIM cards are essentially the brain of your device.
A SIM Card is a chip that all devices carry. The chip that communicates with our network.
SIM Card Innovations
To recognize SIM card differences, you must first understand how the various types work. SIM cards and chip SIMs are two types of SIM card technologies that are commonly used today. We’ll also talk about eSIM technology, which is quickly becoming another SIM connectivity standard.
SIM Cards (UICC)
The most well-known is standard SIM card technology. Universal Integrated Circuit Cards (UICC) are tiny plastic memory chips that fit into a device. SIM cards are commonly used to connect IoT and non-IoT devices such as phones, laptops, tablets, and a variety of other devices. They are usually available in four different SIM card sizes. The required size will be determined by the hardware configuration of your device or devices.
Embedded SIMs (MFF2 UICC) or Chips
MFF2 UICC, also known as embedded SIMs or chip SIMs, are Machine-to-Machine Form Factor Universal Integrated Circuit Cards. The connectivity technology is essentially the same as UICC SIM cards, but the way it is installed differs. Unlike a standard SIM card, which can be slid in and out of a device, a chip SIM is vacuum-sealed and soldered directly onto a device’s circuit board during manufacturing. This permanently installs the SIM chip onto a device, providing some additional advantages. The chip SIM is less likely to be tampered with because it is embedded in the device, adding an extra layer of security.
eSIMs (eUICC)
The new kid on the connectivity block is eSIM technology. An eSIM, also known as an Embedded Universal Integrated Circuit Card (eUICC), converts a traditional SIM card into a digital one. An eSIM can still be found in all of the UICC or MFF2 UICC SIM card sizes, embedded or non-embedded, but it is reprogrammable. With Over The Air (OTA) provisioning, eSIMs make switching between mobile carriers simple. What does this mean for Internet of Things (IoT) and machine-to-machine (M2M) connectivity? Better connections, lower costs, increased security, simplified bulk device management, and other benefits. While eSIMs are still in their infancy, it won’t be long before they become a standard connectivity technology.
The other terms for eSIMs are iSIM, nuSIM, and soft SIM may also be heard, but these are non-standards-based SIM technologies. They are uncertified and may pose security risks. In the short term, it’s best to stick with the three SIM card technologies we discussed for the most reliable and secure IoT connectivity.
What Are SIM Card Sizes?
SIM cards are available in three sizes: standard (mini), micro, and nano. SpeedTalk Mobile includes a free 3-in-1 SIM card with every plan purchase, which means we give you a triple-cut SIM and you pop out the size that fits your device.
There are three basic sizes of SIM card: the standard, the micro, and the nano.
Of the three, the Standard is the original SIM and the largest. Today, these are mainly used on older phones.
The Micro SIM card is essentially a standard SIM card with the extra plastic around the circuit board trimmed off. A trimmed version of the Micro, the Nano is the smallest and used on today’s iPhones. Although minuscule compared to prior versions, the Nano still holds the same amount of data as earlier SIM cards.
Mini-SIM Card
When skimming the evolution of the SIM card, you likely noticed that they’ve become much smaller. But prior to the launch of the iPhone 4 in 2010, we really only had one SIM card size. Introduced in ‘96, it was the standard used in every phone and it made the GSM folks happy. Essentially, it was your entire phone on a card. It made things simple. If you wanted a new phone, all you’d need to do was take that SIM out, pop it into any phone and suddenly your phone number would be transferred to the new device. For over a decade, this was the standard, which made switching phones a breeze. Now? Not so much.
Micro-SIM Card
Like the Apple company. Wanting to save precious room for its newest generation of smartphones, Apple switched from using the standard Mini-SIM to the Micro-SIM once the iPhone 4 hit shelves.
Surprisingly, the Micro-SIM wasn’t some new flashy SIM developed for the latest iPhone. Believe it or not, it was first introduced in 2003.
Back then, its purpose was clear: if a device was too small to fit a mini-SIM, you’d have to use the micro-SIM. In addition, the micro-SIM was designed for backward compatibility, meaning it can work with input generated by an older version of the SIM (such as the Mini-SIM).
In addition, despite its smaller size, the micro’s performance wasn’t impacted at all, as chip’s contact area remained the same. It turned out to be scaled down – the card only needed its excess plastic to be cut from it.
When Apple released the iPhone 4 with the micro-SIM, it became the standard for most smartphones. Samsung, Nokia, and HTC are just a few of the manufacturers that adopted the new Micro-SIM. During this time, several upgrading to the iPhone 4 opted to use an adapter to get their SIM cards cut down to Micro’s, as well.
Nano-SIM Card
If you thought Apple was done using smaller SIM cards, think again. Perhaps Apple was peeved they had to use a SIM card from 2003 on the shiny new iPhone 4. Maybe they just wanted to stay ahead of the curve and throw competitors off their trail.
In any case, the launch of the iPhone 5 prompted the public to realize there was a new SIM in town: the Nano-SIM. This choice to go small made life pretty difficult for users. Anyone upgrading to an iPhone 5 or switching from Android now had to get a new SIM card or an adapter.
Fortunately, most smartphones released since 2014 (both iOS and Android) now support Nano SIM card technology as the standard. Still, it’s sad to see a card that small take over, as it was always much easier changing phones with the Standard SIM compared to the Nano.

eSIM and Soft SIM
Now, where will the SIM card go in the future? Judging from the trend, it’ll likely be the size of a speck of dust, so insignificant that you wouldn’t even feel it in your hand.
No. I’m joking, that would be horrible. But get this: the next version of the SIM likely will be impossible to hold. That’s because it will be entirely virtual.
Cards like the eSIM and the Soft SIM are looking to be the next carnation of the SIM card we’ll see, a software “card” that carries all of the SIM’s original functions without any of the plastic or brass hardware bits.
One cool aspect of this new class of SIMs is that subscribers are able to switch operators easily, without swapping the physical SIM card. Given that this transfer is possible, maybe software-based cards are the answer when it comes to the hassles that came with switching phones over the years.
But despite its conveniences, the eSIM and soft SIM have their fair share of detractors. One potential risk that has been raised by networks regarding these SIMs is the issue of security. With hackings only becoming more prevalent, perhaps it’s hasty to lock all of a subscriber’s credentials and data into the OS of their device without building better cyber defenses against them.
It’s plausible that as the eSIM and Soft SIM are further developed, risks will be addressed until this version of the SIM overshadows the physical SIM, rendering it obsolete. In a way, it’s surprising that the SIM is only at this point of going digital now. As a product of the 1990’s, it’s amazing to consider the SIM card’s evolution, especially when compared to how fast other technologies of the era morphed and died out as newer solutions were innovated. As a link tying together the subscriber’s phone data with their network, the SIM card’s purpose has always been clear – but it will be interesting to watch what another two decades do for the future of this purpose and the SIM card itself.

How To Replace SIM Cards?
Inserting or removing a SIM card is an easy process once you determine where it is stored on your phone. Depending on the type of phone, it could be placed behind the battery. In that case, you will have to open the back panel. For other phones, the SIM cards can be found on the side of the phone.
Removing the SIM card is simple if you have the right tool. Depending on what kind of phone you have, you can easily pop it out of the slot with a paperclip or the edge of something like a credit card. There are some SIM cards that are in easier spots that can slide out with the tip of your finger.
Is installing the SIM card hard?
Not at all, it takes about ten seconds. Take a look at this example of someone placing a SIM card in a phone.
HOW-TO REPLACE A SIM CARD VIDEO
If you are not sure how to insert the SIM card, look up your phone manufacturer’s instructions online or watch a video on how to easily replace the card in the right slot.
Security With Using SIM Cards.
SIM swapping, a hack that has become more common in recent years, is one of the risks associated with SIM cards. Attackers persuade a service provider that the attacker is one of the provider’s existing customers and requests that the victim’s existing account be transferred to a new SIM card purchased by the attacker.
Because providers cannot detect whether a physical device belongs to the account holder other than through SIM cards, this attack results in the victim’s account being transferred to the attacker’s new SIM card, which the attacker can then use on any phone.
SpeedTalk Mobile has a 24-hour call center, and they will ask a series of authentication questions to verify who they believe is their wireless customer. As long as you successfully answer those questions, you can act as if you are the actual customer.
Attackers can obtain the information they need to successfully bypass authentication questions in a variety of ways. Customers whose personal information has been compromised in previous hacks, or customers who have posted relevant information online themselves, can be targeted.
Perhaps your social media is giving away those answers because you have a public profile. Questions might include, ‘Where did you go to high school?’ When is your wedding anniversary? ‘Can you tell me your mother’s maiden name?’ The questions we’re all asked when we sign up for services and add security questions. So You want to be careful and unique with you answers.
Switching Out Your Device SIM Cards for Travel.
Having a separate identifying card from the mobile device has advantages, such as when a phone user travels abroad. Instead of paying high international rates through a home-country phone provider or purchasing an entirely new phone, a traveler can purchase another SIM card for a low price from a carrier that operates within the destination area. All data and applications on the physical device would remain accessible, and the original SIM card could be switched back once the user returned from the trip.
Instead of paying extra for an international plan, it was so simple to simply switch it out. It works perfectly in that country and has a limited amount of data to use. It was almost considered a convenience or a way to save money.
The SIM card of a user can be easily removed from a defective phone and inserted into another device. If the user’s phone dies unexpectedly and they need to receive an important call, the SIM card can be transferred to a friend’s phone and they will continue to receive calls and messages.
While switching SIM cards may be convenient during international travel, there is always the possibility that a removed card will be lost. SIM cards also bind customers to their service providers because switching providers typically necessitates obtaining a new physical SIM card — a simple process, but one that may deter users due to the inconvenience.
Recent developments indicate that the SIM card is most likely here to stay, though its format may change. Apple phones began including two SIM card slots per device in 2018, allowing users to have multiple active phone plans or switch between subscriptions more easily. One of the two SIMs in most phones shipped around the world is a “embedded” SIM, or eSIM, which means there is no physical card that can be removed from the phone. When customers decide to switch carriers, providers can reset the eSIM.
How to Protect Yourself Against SIM Swapping.
After a successful SIM swapping attack, a customer’s phone will no longer function properly. The customer will be unable to make or receive outgoing calls or messages.
As a result, attackers have a limited window of opportunity to use the account before the customer realizes there is a problem — but that doesn’t mean attackers can’t cause significant damage. To authenticate users, many services and websites use phone calls or text messages. Attackers with access to a customer’s account via a new SIM card can circumvent those barriers as well as many two-factor authentication processes.
However, SpeedTalk Mobile providers and customers can take precautions to avoid SIM swapping. PIN numbers are used by SpeedTalk Mobile as an additional layer of security. Following the creation of a PIN with the provider, subsequent changes to the account, such as porting the account to a new SIM card, would necessitate the PIN.
The SIM Card Account PIN code should be one-of-a-kind, something you’ve never used before. If you use a PIN code on your phone and the same one for your ATM, you are more likely to experience identity theft.
It is also critical to be informed and vigilant. The quicker a consumer responds to a SIM swap attack, the less time the attacker has to cause harm. If you suddenly can’t send or receive calls on your phone, you should contact SpeedTalk Mobile right away.
Why SIMs Are Here to Stay
While SIM cards appear to be a part of mobile communications for the foreseeable future, customers may increasingly have accounts with multiple providers at the same time. Customers can choose between juggling two carriers or having a primary provider connected to an eSIM and multiple SIM cards for travel with Apple’s devices.
Or, while eSIMs are just as vulnerable to SIM swapping attacks as regular SIM cards, users don’t have to worry about losing the card and having to reconfigure their account with their primary provider. Finally, it is determined by the type of behavior desired by the customers.
Cellular connectivity is one of the most common and reliable methods of connecting your Internet of Things (IoT) devices. A Subscriber Identity Module, or SIM, is required to connect these devices to a carrier. SIM cards are available in a variety of shapes and sizes. The type of SIM required will be determined by the objective, function, and design of your IoT device.